Reflected-XSS vulnerability municipality of Eindhoven
Jeremy Melis
11-11-2024
introduction
This vulnerability was found during the "Hack Me please" event hosted by the municipality of Eindhoven for students of the Fontys University of Applied Sciences. The event started on the 8th of October and ended on the 8th of November. During this time I found a working reflected XSS vulnerability. This is the write-up for said vulnerability.
(Fixed) exploit
working exploit:
https://werkenvooreindhoven.easycruit.com/career-center/login?iso=')%3b}vartest=alert()%3beval(test)%3b{//
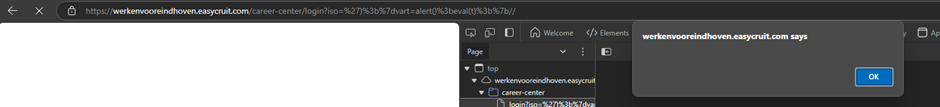
screenshot:
 How it is loaded in the code:
How it is loaded in the code:
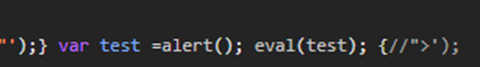
(Line 56, Column 661)
Note: For clarity, the code screenshot uses a different payload with (url-encoded) spaces.
How I found it
Burp Suite identified that XSS was possible by using the ?iso parameter. After testing this, I discovered that the payload used by Burp Suite was reflected in the code. However, it did not trigger the expected popup.
- Burp's payload:
nl16952%27%3balert(1)%2f%2f393
I then located the part of the code where this payload was being processed by searching for alert using Ctrl+F. This led me to Line 56, Column 661 in the code.
Why the popup didn't trigger
The payload didn’t trigger the popup as expected, so I investigated the issue. I removed excess code from the payload and found that only the single quote (') was required to escape the code.
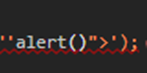
I then tested '<script>alert()</script>, but this didn’t work because the website had blocked the < and > characters.
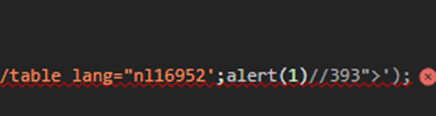
as you can see here:
 To bypass this, I used html encoding for the
To bypass this, I used html encoding for the < and > characters. For example, %3a was used for >, this did not work and during this I also discovered that double quotes (") were blocked as well.
Reading & fixing the code
after reading the code I found that there wasn't a need to use <script> because the part of code I had access to was already surrounded by a <script> tag. See Picture
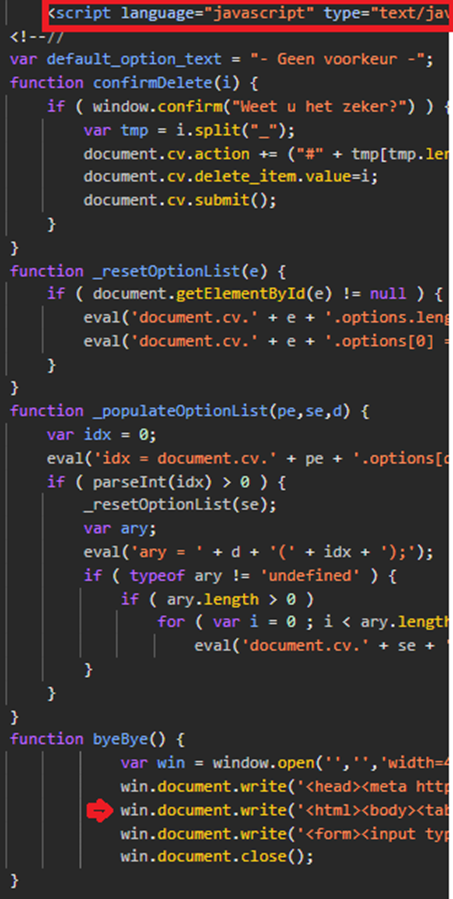
The red highlight shows we are already in a script tag and the red arrow shows the line which we have access to,
I then tried 'alert()
 This showed an error message,
After hovering over the error message, it showed:
This showed an error message,
After hovering over the error message, it showed:
Uncaught SyntaxError: missing ) after argument list
I copied the portion of the website's code where I could inject my own code and pasted it into an HTML test file in Visual Studio Code. I experimented with ways to fix the syntax error, but I didn’t have access to the last part of the line, so I attempted to comment out the remaining code using //.
This made me able to remove the error and allowed me to insert my payload successfully.
Creating payloads
after fixing all the syntax errors in my HTML testing file I came up with the following working payload:
%27)%3b}%20var%20test%20=%20alert()%3b%20eval(test)%3b%20{//
this used %20 which is an url encoded whitespace.
after finding this I tried to come up with a shorter payload by removing all the white spaces and renaming the test variable to t to make it shorter.
this gave me the following payload:
')%3b}vart=alert()%3beval(t)%3b{//
Causes
Like all other XSS vulnerabilities, this vulnerability was caused because of bad user input sanitation. The field I used (?iso) had functionality to change the language of the site, however no button for doing that is located on the site so I think the field was forgotten about.
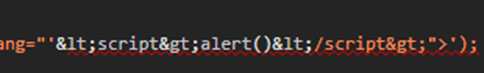
The HTML code where the injection is located tried to comment out the whole JavaScript part but failed in doing this properly. see the picture below
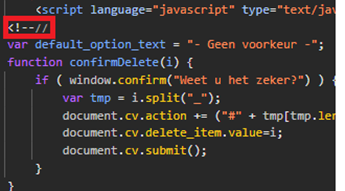
The highlight shows the mentioned comment annotation.
This comment used HTML comments and JavaScript comments together.
<!-- is a HTML comment // is a JavaScript comment. The HTML comment doesn't work because we are already inside of the <script> tag, although the JavaScript comment is valid it only comments out a single line after it, which makes it useless for preventing the payload from triggering.
Impact
After contacting the municipality about this vulnerability I was notified that this caused a internal research in the municipality because the site was published without the proper steps taken. The municipality adjusted the steps so a similiar accident won't happen again. They also notified the creator of the software and the vulnerability was fixed.
Hack me please event
I found this vulnerability while participating in the "Hack Me Please" event hosted by the municipality of Eindhoven for students of the Fontys University of Applied Sciences, where as of writing this I am studying. For finding this vulnerability I won the event with my group, and I personally received a nice painting made by the TISO of the municipality see picture below.
On the left: Rob Mellegers (CISO), on the right: Geert Bax (TISO) of the municipality.
